Linux is known for its stability and security, but no system is completely immune to threats. From unauthorized access to malware attacks, even Linux servers and desktops can be vulnerable if not properly secured. Whether you’re managing a personal system, a business server, or a cloud-based Linux environment, taking proactive steps to protect your data is essential.
From configuring firewalls and managing user permissions to monitoring system activity and encrypting sensitive data, these tips will help you secure your Linux system, prevent security breaches, and ensure your system remains reliable and resilient.
Introduction: Why Linux Security Matters
Linux is widely recognized for its stability, performance, and open-source flexibility, making it the preferred choice for servers, desktops, and critical systems worldwide. From powering web servers and cloud infrastructure to running embedded devices and personal computers, Linux plays a central role in modern technology. However, its widespread use also makes it a prime target for cyber threats, which is why Linux security is not optional—it’s essential.
While Linux is often considered more secure than other operating systems due to its robust permission system and open-source transparency, no system is completely immune to attacks. Hackers, malware, and misconfigured systems can exploit vulnerabilities to gain unauthorized access, steal sensitive data, or disrupt operations. According to the 2023 Linux Foundation Security Report, misconfigurations, outdated packages, and weak authentication mechanisms are among the top reasons Linux systems are compromised, even in enterprise environments.
Understanding and implementing effective Linux security measures is crucial for several reasons.
- Protecting Sensitive Data – Linux systems often host confidential information, such as personal data, corporate records, or financial information. A single breach can lead to data loss, regulatory penalties, and reputational damage.
- Preventing Unauthorized Access – With remote access capabilities like SSH, Linux servers are exposed to the internet, making them vulnerable to brute-force attacks or unauthorized login attempts.
- Maintaining System Integrity – Cybercriminals can exploit vulnerabilities to install backdoors, malware, or rootkits. Ensuring proper security practices prevents such tampering.
- Ensuring Service Availability – Many businesses rely on Linux servers for critical services. A security incident can result in downtime, financial loss, and operational disruption.
Securing a Linux system involves a multi-layered approach: keeping the system updated, configuring firewalls, managing user privileges carefully, encrypting sensitive data, and monitoring system activity for anomalies. adopting these 12 essential security tips, Linux users whether beginners or experienced system administrators can significantly reduce risks and ensure their systems remain resilient against evolving threats.
1. Keep Your System Updated: Apply Security Patches Regularly
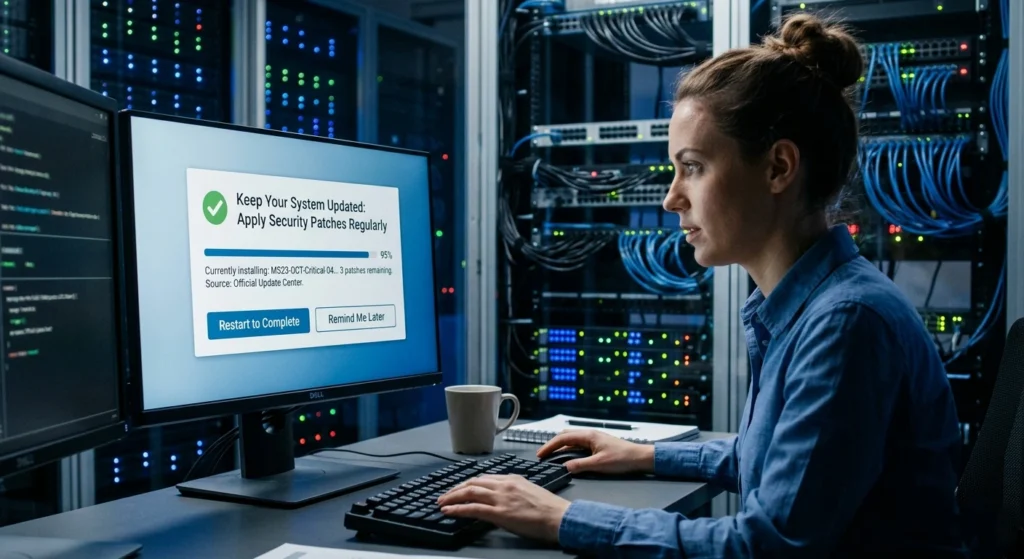
One of the most fundamental practices for Linux security is keeping the system and its software up to date. Security patches are released to fix vulnerabilities, close exploits, and enhance system stability. Neglecting updates is one of the primary causes of breaches, as attackers often target outdated packages with known vulnerabilities.
Why Updates Are Critical
Linux distributions release frequent security patches for the kernel, libraries, and applications. Missing updates can leave your system exposed to.
- Privilege escalation exploits
- Remote code execution attacks
- Denial-of-service vulnerabilities
for example, the Dirty Pipe vulnerability (CVE-2022-0847) affected Linux kernels before version 5.16.11, allowing local users to overwrite read-only files a clear demonstration of why prompt patching is essential.
Best Practices for Updating
1: Enable automatic security updates: Most distributions allow automatic patching of critical packages.
- On Ubuntu/Debian:
sudo apt update && sudo apt upgrade -y- On Fedora/CentOS/RHEL:
sudo dnf update -yKeeping your system updated is the simplest yet most effective layer of defense against attacks.
2. Use Strong Passwords and Multi-Factor Authentication

Weak passwords remain a primary vulnerability for Linux systems. Even with a secure system, a simple password can allow unauthorized access, especially on SSH-enabled servers.
Creating Strong Passwords
- Use long, complex passwords with a mix of uppercase, lowercase, numbers, and symbols.
- Avoid predictable patterns like
123456orpassword. - Consider passphrases with random words for memorability.
Implement Multi-Factor Authentication (MFA)
Adding MFA adds an extra layer of security, ensuring that even if a password is compromised, unauthorized access is prevented.
- SSH MFA: Use tools like Google Authenticator or YubiKey for SSH logins.
- System login MFA: PAM (Pluggable Authentication Modules) supports MFAfor local and remote logins.
Enforcing Password Policies
- On Linux, configure
/etc/login.defsto set minimum password length and expiration periods. - Enable account lockouts after repeated failed attempts to prevent brute-force attacks.
Strong passwords combined with MFA are non-negotiable forsecure Linux environments, especially servers exposed to the internet.
3. Limit Root Access and Use the Principle of Least Privilege
Linux’s root account has unrestricted access, which makes it a prime target for attackers. Minimizing root usage reduces the risk of accidental or malicious damage. Limiting root access is one of the most important steps to secure your Linux system. principle of least privilege, you ensure that users and applications only have the permissions they need, reducing the risk of accidental or malicious system changes.
Principle of Least Privilege
- Assign only the necessary permissions to each user or service.
- Avoid using root for everyday tasks.
- Use
sudoto grant temporary elevated privileges.
Best Practices
- Create individual user accounts for each administrator.
- Configure
sudopolicies to restrict command execution. - Audit
/etc/sudoersregularly to remove unused privileges.
Limiting root access ensures that a compromised account cannot wreak widespread damage.
4. Enable and Configure a Firewall for Added Protection
A properly configured firewall can block unauthorized traffic before it reaches your Linux system, serving as a critical line of defense. Enabling and properly configuring a firewall is a key step in protecting your Linux system from unauthorized access and cyber threats.
A firewall controls incoming and outgoing traffic, helping to block malicious activity while allowing legitimate connections, giving your system an essential layer of security.
Linux Firewall Tools
- UFW (Uncomplicated Firewall) – user-friendly for Ubuntu and Debian-based systems.
- Firewalld – default in Fedora, CentOS, and RHEL.
- iptables – advanced configuration for custom rules.
Best Practices
- Block all incoming traffic by default and only allow necessary services (SSH, HTTP/HTTPS).
- Restrict SSH access to specific IP addresses.
- Regularly review firewall logs to detect anomalies.
A firewall is your first line of defense against network-based attacks.
5. Install and Maintain Security Software and Antivirus Tools
Although Linux is less prone to malware than Windows, it is not immune. Security software helps detect rootkits, trojans, and suspicious behavior. Installing and regularly updating security software and antivirus tools is crucial for keeping your Linux system safe from malware, viruses, and other cyber threats.
Recommended Tools
- ClamAV – open-source antivirus for scanning files.
- rkhunter and chkrootkit – tools to detect rootkits.
- Auditd – tracks system events for suspicious activity.
Best Practices
- Regularly scan critical directories for malware.
- Automate security audits and reporting.
- Keep definitions and tools up to date.
Regular monitoring with security software ensures early detection of threats.
6. Secure SSH Access and Use Key-Based Authentication
SSH provides remote access to Linux systems, making it a common attack vector if not secured properly. Securing SSH access is essential to prevent unauthorized remote logins to your Linux system. Using key-based authentication instead of passwords adds a strong layer of security, making it much harder for attackers to gain access while keeping remote management safe and efficient.
Steps to Secure SSH
SSH provides remote access to Linux systems, making it a common attack vector if not secured properly.
Steps to Secure SSH
- Disable root login over SSH.
- Edit
/etc/ssh/sshd_config:
- Edit
PermitRootLogin no2: Use SSH key-based authentication instead of passwords.
- Generate keys:
ssh-keygen -t ed25519 -C "user@example.com"3: Change default SSH port to reduce automated attacks.
4: Enable fail2ban to block repeated failed login attempts.
SSH security is critical; compromising it can grant complete control over your system.
7. Monitor System Logs and Set Up Alerts for Suspicious Activity
Monitoring logs is essential for early threat detection. Monitoring system logs and setting up alerts helps you detect suspicious activity early on your Linux system. regularly reviewing logs and automating notifications, you can quickly respond to potential security threats and maintain a secure, well-protected environment.
Important Logs
/var/log/auth.log– login attempts/var/log/syslog– system events/var/log/secure– security-related logs
Best Practices
- Use logwatch or logrotate to manage logs efficiently.
- Configure email alerts for suspicious events.
- Review failed login attempts, sudo usage, and system errors regularly.
Continuous monitoring transforms Linux security from reactive to proactive.
8. Regularly Backup Your Linux System and Data
Backups are a critical component of security, ensuring you can recover from hardware failure, ransomware, or accidental deletion. Regularly backing up your Linux system and data is a crucial step in security and disaster recovery. Backups ensure that, in the event of hardware failure, malware attacks, or accidental deletion, you can quickly restore your system and protect important files.
Best Practices
- Use full, incremental, and differential backups.
- Store backups offsite or in the cloud.
- Test recovery procedures regularly.
A secure system is only as good as your ability to restore data in case of a breach or failure.
9. Disable Unnecessary Services and Applications
Every running service is a potential attack surface. Reducing unnecessary services minimizes exposure. Disabling unnecessary services and applications reduces potential attack surfaces on your Linux system. turning off features you don’t need, you minimize security risks, improve system performance, and make your Linux environment safer and more efficient.
How to Harden Services
- List running services:
systemctl list-units --type=service- Disable unused services:
sudo systemctl disable service_name- Audit cron jobs and background processes.
The fewer unnecessary services running, the smaller the attack surface.
10. Encrypt Sensitive Data and Files on Your System
Data encryption ensures that even if files are stolen, they remain unreadable without the key. Encrypting sensitive data and files on your Linux system adds a vital layer of security. Even if unauthorized users gain access, encryption ensures your personal and business information remains protected and unreadable without the proper keys.
Linux Encryption Tools
- LUKS – encrypt entire partitions.
- GnuPG – encrypt individual files.
- eCryptfs – encrypt home directories.
Best Practices
- Always encrypt backups and removable media.
- Use strong, complex passphrases for encryption keys.
- Combine encryption with access control.
Encryption is the last line of defense if physical or remote breaches occur.
11. Practice Safe Software Installation and Package Management
Installing software from trusted sources prevents malware introduction. Practicing safe software installation and careful package management is essential for Linux security. using trusted repositories, verifying software sources, and avoiding unverified packages, you reduce the risk of malware, vulnerabilities, and system compromise.
Best Practices
- Use official repositories (apt, dnf, yum, or zypper).
- Avoid running scripts from unverified sources.
- Verify package signatures:
gpg --verify package.sig package.tar.gz- Remove unused packages to reduce vulnerabilities.
Safe package management protects Linux from supply chain attacks.
12. Stay Informed: Follow Security News and Best Practices

The threat landscape evolves constantly. Staying informed is essential to anticipate and prevent attacks. Staying informed about the latest security news and best practices is key to your Linux system secure. Regularly following updates, vulnerabilities, and expert advice helps you proactively protect your system from emerging threats.
Best Practices
- Subscribe to Linux security mailing lists:
- Ubuntu Security Notices
- Fedora Security Announcements
- openSUSE Security Announcements
- Follow Linux security blogs and vulnerability databases (CVE, NVD).
- Participate in security communities for tips and shared experiences.
Knowledge is power the more you stay informed, the better you can defend your system.
Conclusion: Keep Your Linux System Safe and Resilient
Securing your Linux system is a continuous process, not a one-time setup. following these 12 essential security tips from keeping the system updated and enforcing strong passwords, to monitoring logs, encrypting data, and staying informed you can dramatically reduce risk, maintain system integrity, and protect sensitive data.
Implementing layered security, regularly auditing your system, and fostering good security habits ensures that your Linux environment remains robust, resilient, and prepared for evolving threats.
Remember: security is not a feature it’s a mindset. A well-secured Linux system is the foundation of a safe, efficient, and trustworthy computing environment.