Personal data is more valuable than ever. Every time you browse a website, download an app, shop online, or interact on social media, pieces of your digital identity are being collected, stored, analyzed, and sometimes even shared. From your location and browsing habits to financial details and biometric data, the modern internet runs on information and much of that information is yours.
Data privacy discussed by cybersecurity experts.
Data privacy is no longer just a technical issue discussed by cybersecurity experts. It has become a daily concern for individuals, families, businesses, and governments worldwide. With the rapid growth of artificial intelligence, smart devices, cloud services, and connected platforms, personal data flows across systems faster and more widely than ever before.
While these innovations bring convenience and personalization, they also increase the risks of data breaches, identity theft, surveillance, and misuse of sensitive information.
Protecting personal data requires advanced technical knowledge.
Many people assume that protecting personal data requires advanced technical knowledge. safeguarding your online privacy starts with awareness and smart habits. how companies collect data, what permissions you grant to apps, how secure your passwords are, & how your information is shared across platforms can dramatically reduce your exposure to risk.
How to Safeguard Your Personal Information in the Digital Age
In 2026, the volume and value of data generated each day continue to increase. According to recent studies, individuals now create over 2.5 quintillion bytes of data each day with a significant portion containing personal details such as names, locations, and online behaviors.
Why Personal Information Is Valuable
Personal data is often referred to as the “new oil.” Companies and organizations use.
- Personalized advertising
- Predictive analytics
- Improving service offerings
- Enhancing user experiences
But when data falls into the wrong hands, the consequences can include identity theft, financial loss, and long-term privacy violations.
Major Threats to Personal Data Today
Modern digital threats are not limited to traditional viruses.
include.
- Deceptive Attacks: Fraudulent messages designed to trick you into revealing credentials.
- Data Breaches: When large collections of user data are exposed from corporations or platforms.
- Unsecured Networks: Public Wi-Fi can allow attackers to intercept your data.
- Third-party Tracking: Many apps collect information without explicit user awareness.
- Malware & Spyware: Software that secretly collects information or controls parts of your device.
Each of these threats targets personal information in different ways. Recognizing the risks helps you take proactive steps to protect yourself.
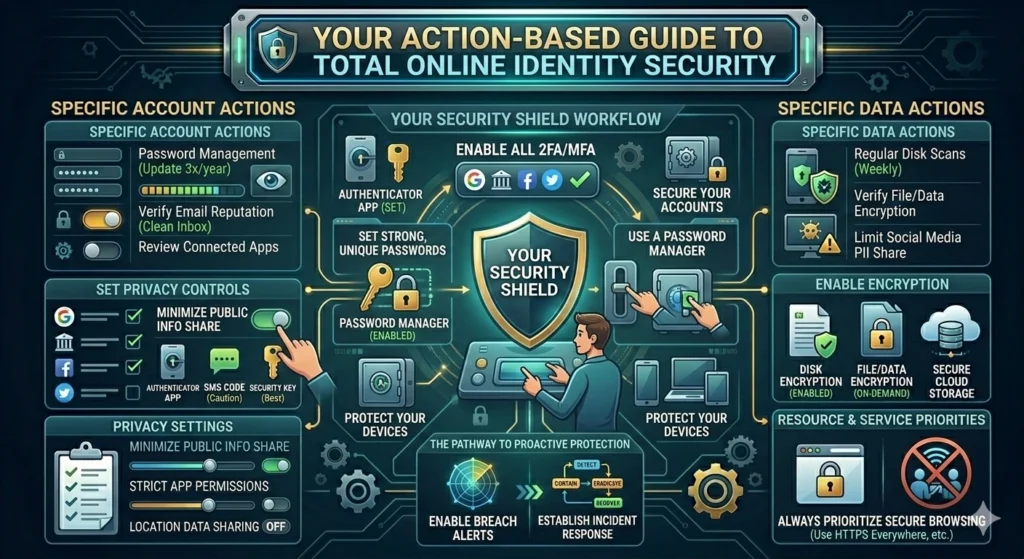
Foundational Steps to Protect Personal Information
To safeguard your data effectively
- Use Unique Passwords for every account
- Enable Two-Factor Authentication (2FA)
- Regularly Review Privacy Settings
- Stay Updated on Security News
Maintaining awareness of how your data is collected and used strengthens your digital defenses.
Protecting Your Online Identity in an Increasingly Connected World
Personal identity online extends far beyond your name and email. It includes digital behavior, preferences, location data, and even seemingly minor details like browsing habits. We live in a world where almost everything is connected our phones, laptops, smart home devices, cars, and even wearable technology.
While this constant connectivity makes life more convenient, it also means your online identity is exposed to more risks than ever before. Every account you create, every app you install, and every website you visit leaves behind digital traces that can be tracked, stored, or even exploited.
Protecting your online identity today goes far beyond creating a simple password. It requires awareness, smart security habits, and an understanding of how your personal information moves across the internet.
From social media profiles and banking details to browsing history and location data, your digital footprint tells a detailed story about who you are.
The Complexity of Modern Online Identity
Every time you interact with an app or service, you are creating a digital persona a collection of data points that, when combined, reveal far more than just surface details.
For example.
- Purchase history
- Search queries
- Preferred times of internet activity
- Social media interactions
These data points jointly construct a unique profile of who you are and how you behave online.
Risks of an Exposed Digital Identity
A compromised digital identity can result.
- Impersonation attacks
- Fake accounts under your name
- Financial fraud
- Loss of reputation
Identity theft remains one of the most damaging online risks. In the recent years, millions of people worldwide have reported incidents where their personal credentials were used without authorization.
Best Practices to Protect Your Digital Identity
Protecting your identity online requires a layered approach.
1. Minimize Public Exposure
- Review your social media privacy settings.
- Avoid sharing sensitive information publicly.
- Don’t post your full date of birth, home address, financial details, or other personally identifying details.
2. Secure Your Account Recovery Information
Always ensure that your email address and security questions are updated and unique.
3. Beware of Social Engineering
Threat actors often masquerade as trusted entities to extract data. Always verify the sender’s legitimacy before responding.
Essential Strategies to Keep Your Personal Data Secure Online
Personal data security demands intentional actions. Below are widely recommended strategies that are effective in 2026 and beyond. Keep your personal data secure online is no longer optional it’s a necessity.
From social media accounts and online banking to shopping websites and cloud storage, your sensitive information is constantly being transmitted across digital platforms. Without proper protection, this data can become vulnerable to hackers, scams, and unauthorized access.
The key to staying safe lies in adopting smart, practical strategies that strengthen your digital security.
Here are some essential steps you should follow..
- Use secure Wi-Fi connections or a VPN when accessing sensitive information on public networks.
- Use strong, unique passwords for every account and store them securely with a trusted password manager.
- Enable two-factor authentication (2FA) to add an extra layer of account protection.
- Regularly update your devices and software to patch security vulnerabilities.
- Be cautious of Deceptive emails and suspicious links that attempt to steal your credentials.
- Limit the personal information you share online, especially on social media platforms.
- Review app permissions and remove access to data that isn’t necessary.
Use Strong, Unique Passwords
- Never reuse passwords across multiple accounts.
- Aim for long passwords – at least 12 characters with a mix of letters, numbers, and symbols.
- Avoid predictable phrases or sequential patterns.
Enable Two-Factor or Multi-Factor Authentication
Two-factor authentication (2FA) adds an extra layer of protection by requiring.
- A password or PIN
- A secondary verification such as a code sent to your phone or generated by an authenticator app
Even if someone guesses your password, 2FA can prevent unauthorized access.
Regularly Monitor Account Activity
Most major services now offer activity logs that allow you to see recent login attempts, connected devices, and any unusual behavior. Checking these logs helps identify unauthorized access early.
Keep Software Updated
Cybercriminals often exploit vulnerabilities in outdated software. Operating systems, web browsers, apps, and plugins should always be updated to the latest versions.
Use Secure, Private Networks
Public Wi-Fi networks are often insecure. Whenever possible:
- Use a trusted home network.
- If using public Wi-Fi, avoid accessing sensitive accounts.
- Consider a secure connection (more on this later).
Stay Safe Online: Practical Steps to Secure Your Digital Footprint
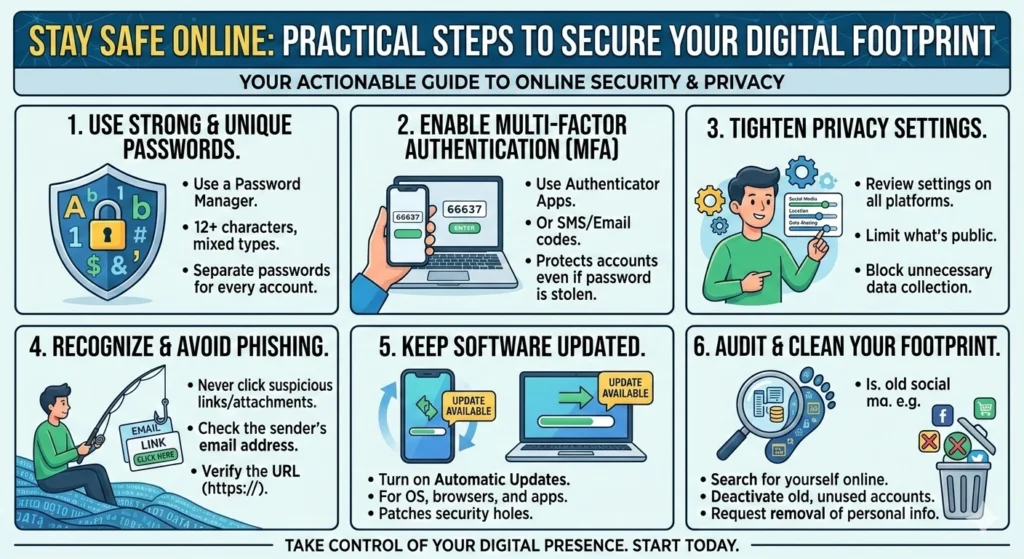
Your “digital footprint” refers to all the traces of data you leave online everything from search history to social media posts. Every action you take online leaves a trace. From the websites you visit and the posts you share to the accounts you create and the purchases you make, your digital footprint continues to grow every day.
While much of this activity feels harmless, it can reveal more about you than you might expect including personal preferences, habits, location data, and even financial details.
Staying safe online starts with understanding how visible your information really is. Cybercriminals, data brokers, and even legitimate companies collect and analyze digital behavior to build detailed profiles. Without proper precautions, this information can be misused, exposed in data breaches, or exploited through scams and identity theft.
Securing your digital footprint ..
Securing your digital footprint doesn’t require advanced technical skills. It’s about taking practical, consistent steps reviewing privacy settings, limiting oversharing, strengthening account security, and being mindful of where and how you share personal data. With the right habits, you can reduce your exposure and maintain better control over your online presence in an increasingly connected world.
Understand Your Digital Footprint
There are two types of digital footprints
- Passive Footprints: Data collected without your active contribution such as tracking cookies.
- Active Footprints: Data you intentionally share, like posting photos or filling out forms.
Awareness of both types helps you manage what you reveal.
Regularly Audit Your Online Presence
Perform the following reviews every few months
- Search your name online
- Check social account privacy settings
- Review apps connected to your accounts
- Delete unused accounts
This protects against unwanted exposure and reduces the amount of data stored about you online.
Limit Permission Requests
Apps and websites often ask permission to access
- Contacts
- Location
- Camera
- Microphone
Only grant permissions that are necessary for functionality. Disabling unnecessary access minimizes potential data misuse.
Be Cautious With Email and Messaging
Deceptive remains one of the most prevalent online threats.
To manage..
- Never open suspicious attachments
- Confirm sender identity before responding
- Watch for irregular URLs and misspelled domain names
Understanding Modern Online Security and Personal Data Protection
Online security has evolved significantly in the past decade. In 2026, people have far more tools and capabilities to protect their data but the stakes are also higher. digital age, online security and personal data protection are more important than ever.
Every time you browse the web, use apps, or shop online, your information is being collected, stored, and sometimes shared. From passwords and financial details to personal habits and location data, modern technology constantly generates sensitive information that needs safeguarding.
Understanding how online security works and the steps you can take to protect your data is essential for staying safe in this interconnected world. It’s not just about preventing hacks it’s about controlling who has access to your information, reducing vulnerabilities, and making informed decisions about your digital presence.
Key Principles of Data Protection
Modern data protection centers around
- Confidentiality: Ensuring only authorized parties can access data
- Integrity: Guaranteeing that data remains unaltered and authentic
- Availability: Authorized users can access necessary data when needed
These principles form the backbone of cybersecurity standards worldwide.
Legal Frameworks That Impact Personal Data
Numerous data privacy laws have been implemented internationally.
Some of the most influential include..
- The General Data Protection Regulation (GDPR) – Europe
- California Consumer Privacy Act (CCPA) – United States
- Data Protection Acts in Canada, Australia, and other regions
These regulations require companies to protect user data and provide transparency about data usage.
How Companies Are Held Accountable
Organizations must.
- Provide data access rights
- Allow data deletion (“right to be forgotten”)
- Report breaches within mandatory timeframes
If mishandled, companies can face significant penalties under modern personal data privacy laws.
Smart Ways to Defend Your Privacy in Today’s Internet Landscape
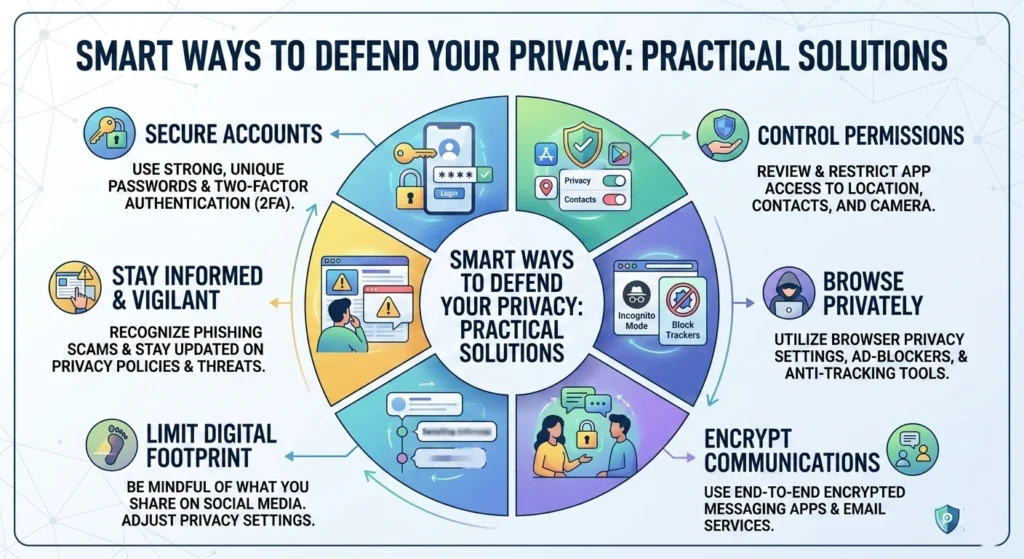
Digital privacy is not just about securing accounts it’s about controlling how your data is collected and used. internet landscape, your personal information is constantly at risk. social media platforms and online shopping to mobile apps and cloud services, & about your habits, preferences, and identity is being collected, stored, and sometimes shared.
Defending your privacy doesn’t have to be complicated. smart strategies such as managing permissions, using strong passwords, securing your devices, and being mindful of the information you share you can significantly reduce your digital footprint and protect yourself online. proactive steps ensures that your personal data stays private, giving you control over your digital life in a world that is more connected than ever.
Adopt a Privacy-First Mindset
Ask yourself
- What data do I need to share?
- Who will have access to it?
- How long will it be stored?
This perspective helps you decide whether sharing certain information is worth the risk.
Adjust Browser Privacy Settings
Browsers now offer strong privacy controls
- Disable third-party cookies
- Block tracking scripts
- Use privacy-focused extensions
Browsers like Firefox and Brave have advanced tracking protection features built in.
Be Mindful of Smart Devices
Internet-connected devices like smart speakers and wearables collect a lot of personal data often continuously.
Before using any new device..
- Read privacy policies
- Review data retention practices
- Disable non-essential data collection features
Choose Services That Respect Privacy
While major platforms dominate the digital space, not all prioritize privacy equally. Where practical, consider services with transparent data policies and minimal tracking.
Everything You Need to Know About Securing Your Digital Life
Securing your digital life extends across devices, accounts, apps, and online environments. Securing your digital life is essential in a world where personal data is constantly collected and shared. from passwords and devices to online accounts and privacy settings, every aspect of your online presence matters.
The key practice like using strong authentication, managing permissions, and staying alert to cyber threats can protect your identity, finances, and personal information. Taking control today ensures your digital life remains safe, private, and under your control.
Protecting Mobile Devices
Mobile devices are primary digital hubs for many people.
Steps to secure.
- Enable automatic locking (PIN or biometric)
- Keep software up to date
- Avoid installing apps from unknown sources
- Check app permissions
Secure Cloud Storage Practices
Cloud storage is convenient, but it can expose data if not protected.
- Use strong, unique passwords for cloud accounts
- Enable encryption where possible
- Avoid storing highly sensitive files unless absolutely needed
Family and Shared Device Safety
Privacy is not just individual it extends to households.
- Teach family members about strong password
- Separate personal accounts and profiles on shared devices
- Set up parental control where necessary
Building Strong Online Privacy Habits for the Future
A strong digital privacy foundation isn’t a one-time effort it’s an ongoing practice. Protecting your privacy online is not a one-time task it is about developing habits that keep your personal data safe over time.
Small consistent actions can make a huge difference in securing your digital life and reducing the risk of identity theft, hacking, or data misuse.
Here are essential habits to adopt for stronger online privacy.
- Keep your software and devices updated to patch security vulnerabilities.
- Use strong, unique passwords for every account and update them regularly.
- Enable two-factor authentication (2FA) wherever possible.
- Limit the personal information you share on social media and apps.
- Regularly review privacy settings on all platforms and devices.
- Be cautious with public Wi-Fi and consider using a VPN.
Think before clicking links or downloading attachments from unknown sources.
Regular Privacy Check-ins
Plan quarterly reviews.
- Update passwords
- Revoke unused app permissions
- Clear old accounts
- Review security settings on primary platforms
Stay Informed
Digital threats change rapidly. Subscribe to reputable cybersecurity news sources to stay updated on emerging risks.
Educate Others
Sharing best practices with friends, family, and colleagues improves collective security.
Conclusion
Protecting personal data in 2026 requires awareness, intentional habits, and strong online hygiene. From securing passwords and enabling authentication to monitoring digital footprints and understanding privacy laws, these practices prevent unauthorized access and preserve your right to online privacy.
Making smart privacy decisions today builds a more secure digital life tomorrow not just for you, but for everyone you interact with in the connected world.